Before we get into examples of using these technologies, I want to make sure you know how to access them as well as provide some tips for using them.
By Carol Woodbury
Editor's Note: This article is excerpted from chapter 1 of the NEW security book, Mastering IBM i Security, by Carol Woodbury.
IBM i Access Client Solutions
Access Client Solutions (ACS) is the client software IBM provides for us to access IBM
i. I am shocked when I repeatedly see IBM i shops continuing to use the ancient Client Access for Windows software. You must migrate to ACS if you haven’t already done so! It’s only a matter of time before Microsoft issues a patch that breaks the software or there’s a new security vulnerability identified that affects the product. Because IBM no longer supports it, you’ll then be scrambling to migrate your users to ACS. Do you really want to be explaining to your management why you’re running software that hasn’t been supported in literally years and are now panicking when you could have had a controlled rollout of the currently supported product? And just because you’re running ACS doesn’t mean you shouldn’t pay attention to IBM Security Bulletins. Older versions of ACS have been identified as being exposed to the log4j vulnerability. In other words, you need to stay current! OK, I’ll get down off my soapbox now and explain some features of ACS.
While I use many of the ACS features, the main feature I’ll be using throughout this book is Run SQL Scripts. See Figure 1.1.
Figure 1.1: Run SQL Scripts in Access Client Solutions.
Launching Run SQL Scripts opens a window that allows you to run SQL that you write as well as take advantage of the SQL examples IBM provides and–bonus!–save your work so you don’t have to re-create the SQL every time you want to run it.
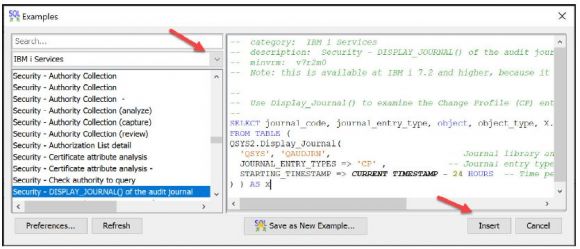
First, let’s see how you can take advantage of the shipped examples. After launching Run SQL Scripts, go to the toolbar and choose Edit > Examples > Insert from Examples. Using the dropdown list, choose IBM i Services. I’ve scrolled down to the Security section of the list. Clicking on the name of the service produces an SQL example in the right window as shown in Figure 1.2.
Figure 1.2: Use Insert to add the SQL example to your Run SQL Scripts window.
I learned how to write SQL by first using these examples. I found an example that was close to what I wanted, clicked on the Insert button to add it to my Run SQL Scripts window, and either ran it as is or, more often, modified it to meet my needs. I encourage you to check out these examples, especially if you’re an SQL novice.
The second feature I want to point out in Run SQL Scripts is the ability to save your work. I know that, as an administrator, you don’t have time to re-create your SQL every time you want to use it. To save your work, click on File in the toolbar, then Save As> PC File. You can save the file on your PC or on a common server so your teammates can also access the file. To use the saved file, click on File > Open > PC File. I use this feature ALL.THE.TIME. I have one saved for each presentation in which I’m using SQL examples, I’ve created files for clients and then sent the file to the client for their use, I have another file that I use when investigating new features but don’t want to start from scratch, and so on. In fact, I have saved the SQL examples used throughout this book and you can download and use them yourself!
Finally, many times the results of running the SQL statement need further review or analysis. When this happens, I send the results to a spreadsheet. Here are the directions to accomplish this. Depending on the version of ACS, you’ll either choose Options from the toolbar and then Enable Save Results… > For This Session. Rerun your SQL, click on a cell in the output section, right-click, and choose Save Results. Or for more recent versions of ACS, choose Edit > Preferences. Then, on the General tab, check the box labeled Enable Saving of Results and click OK. In this case, you’ll have to close down your Run SQL Scripts window, reopen it, rerun your SQL, right-click on a cell in the output section, and choose Save Results.… Or right-click on the Results tab (the tab at the bottom of Run SQL Scripts that shows the SQL that was run) and you’ll also get the Save Results option. With either method, you’ll see various formats you can save your output to (.txt, .csv, .xlsx, etc.) as well as be able to specify where the output is to be saved. Saving the results to a spreadsheet allows me to send the results of my analysis to my clients for their review, allows me to document a “before” picture before changes are made, provides documentation for submission to a change-management committee to document upcoming changes, and more. I’m sure you’ll find many ways to use this feature!
New Navigator for i
Next, the new Navigator for i browser-based interface. “New Nav” as it’s fondly referred to first became available in Technology Refreshes (TRs) IBM i 7.3 TR11 and IBM i 7.4 TR5. At that time, it wasn’t the default, and you had to access it using the URL http:// your-system-name:2002/Navigator/login. But as of IBM i 7.5 and IBM i 7.3 TR12 and IBM i 7.4 TR6, New Nav has officially replaced Heritage Nav (the politically correct term for the old, and quite frankly ugly, previous Navigator for i interface). Now, using the URL http://your-system-name:2001 or clicking on the Navigator for i feature in Access Client Solutions (ACS) will launch New Nav.
One of my goals is to show you how to take advantage of this new and improved interface. If you happen to be on a system that is still using Heritage Nav, I encourage you to upgrade as soon as possible, not only to take advantage of the examples I’m going to show you but also to distance yourself from any vulnerabilities that may be identified in the future but not fixed (since Heritage Nav is no longer supported by IBM). To keep up to date with information regarding New Nav, see https://www.ibm.com/support/pages/node/6483299.
IBM i Services
I’ll be using IBM i Services extensively in this book, so I suggest that you bookmark a couple of websites. One is the support page that lists all of the services that are available as well as the release/Technology Refresh in which they were introduced: https://www.ibm.com/support/pages/node/1119123
Services are categorized by the area of the system to which they pertain—for example, Journal Services, PTF Services, Security Services, etc. (Hint: Sometimes I find it easier to find the service I’m looking for by searching the webpage using a specific term rather than attempting to find the service in its category.) If you click on the name of a service, you may be taken to an intermediate page that lists any updates to the service along with a link to its IBM Information Center page. If no updates, you’ll be taken directly to the service’s page on the IBM Information Center, which details the purpose of the service, the output that will be generated, and, at the very bottom of the page, an example of using the service. An added benefit: if you want to use the SQL example they’ve provided, you can easily click on the icon in the upper right corner of the box containing the example to add the SQL to your clipboard!
New and enhanced services are being provided with each new version of IBM i but also with most, if not all TRs. Here’s one website that helps me keep track of the enhancements: https://www.ibm.com/support/pages/node/1116645/
Authority Collection
Several of my examples will show how to use Authority Collection. Authority Collection for user profiles was introduced in IBM i 7.3 and enhanced to provide collection of individual objects in both libraries and directories in IBM i 7.4. If you’re unfamiliar with the concept and configuration of the Authority Collection feature, I suggest that you read Chapter 16 in my book IBM i Security Administration and Compliance, Third Edition for details.
IBM i Audit Journal
Since the introduction of Authority Collection, I don’t use the audit journal as much as I used to, but it remains a vital tool for investigating and solving security issues. I’ll be showing numerous examples of its use throughout this book. Again, if you are unfamiliar with the basic concepts of the IBM i audit journal, please see Chapter 15 in IBM i Security Administration and Compliance, Third Edition. I will be using both the Copy Audit Journal Entry (CPYAUDJRNE) command, which I describe extensively in my book, as well as the IBM i audit journal table functions that allow me to bypass gathering the information into an outfile and allow me to use SQL to get information directly out of the audit journal.
I prefer using the table functions for a couple of reasons. First, I may be looking for entries for only one specific user or object, but when using CPYAUDJRNE I first must gather all entries of that type. The other reason I prefer using the SQL table functions is that timestamp arithmetic is so easy using SQL. You’ll understand what I mean when you see the examples I provide. It’s likely I would switch and never use CPYAUDJRNE again, but IBM hasn’t yet provided the SQL table functions for all audit journal entry types. You can keep track of which audit journal types are supported at the following link (simply substitute the 7.5 for the 7.X version you’re running): https://www.ibm.com/ docs/en/i/7.5?topic=services-audit-journal-entry. Check this after each TR as this is not a static list! IBM has provided most of these table functions via TRs.
Finally, New Nav has added the ability to examine the audit journal. If you’re new to the audit journal, or even if you’re not, this is an easy way to examine audit journal entries without having to know one iota of SQL! In this book, I’ll show examples of using New Nav to examine the audit journal.
Want to learn more? You can pick up Carol Woodbury's book, Mastering IBM i Security, at the MC Press Bookstore Today!

















 IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
LATEST COMMENTS
MC Press Online