Editor’s Note: This article was previously published on Midrange Computing’s AS/400 Network Expert Web site at www.midrangecomputing. com/ane/99/01.
Enhancements to the Client Access/400 Operations navigator tool makes maintaining AS/400 system security values simple. Use this new feature the next time you need to change or review system security values, and you'll learn more about AS/400 security in a few minutes than you would in a week of reading manuals.
IBM has been doing an outstanding job lately of creating new tools to help us to perform our jobs more easily. For example, the new portable configurator, which can be downloaded from the IBM AS/400 Service Web site at www.as400service.ibm.com, allows you to easily configure a new AS/400 system on your PC. This is much easier than trying to navigate through the old 3270-based configuration tool you’ve to grown to dread using. With the release of Client Access/400 for Windows 95/NT V3R2, IBM has added to its growing list of user-friendly, intuitive client-side tools. The latest version of AS/400 Operations Navigator in V3R2 has many new features, including some very helpful wizards. In this article, I’m going to take a look at the new Security Wizard and step you through how to use it to configure security on your AS/400.
A Truly Useful Tool
IBM designed the Operations Navigator program to be used as a tool from which you can monitor and control various system values and functions. It has the Windows 95/NT Explorer look and feel, so, if you’ve ever used Windows Explorer, you’ll feel comfortable with this GUI as well. Client Access/400 V3R2 incorporates many new features, making it truly useful. The new AS/400 Security Wizard is a great example. You access this new wizard by opening the new Operations Navigator and right-clicking on the Security icon. You’ll see a dialog box open with several options in it. Select the one labeled Configure and you’ll be presented with a panel like the one shown in Figure 1.
This wizard will create a set of security recommendations for your AS/400, create reports explaining the security recommendations, and, optionally, apply those changes on your AS/400. The ultimate result of using this wizard will be to change/set System Security Values on your AS/400.
How Do You Use Your System?
As you step through the various panels, you are asked a series of questions about how you use your AS/400 as well as what level of security you think you will need. Many of these questions are intuitive rather than simple yes/no questions. For those of you who are used to working with the AS/400 System Values and their finite responses, this new heuristic approach may take some getting used to.
For example, you will be asked how you would characterize the general security policy on your AS/400. You can choose from characterizations such as Strict, Average, or Relaxed. These choices relate, roughly, to the various system security levels (10, 20, 30, 40, or 50). Your responses determine the outcome of the recommendations in the reports generated by this wizard. For example, if you said that your overall security policy was relaxed, the recommendation may be to set the security level to 20. If you said that your security policy was strict, the wizard would probably recommend that your security level be set to 40. A response to any one of the Security Wizard’s dialog panels does not control the final recommendation. Rather, the final report is based on the combination of all of your responses.
There are a variety of questions you’ll be prompted to answer. Many of them require simple yes/no responses:
• Does your AS/400 have workstations that are easily accessible by individuals who are not authorized to the system?
• Does your AS/400 use Advanced Program-to-Program Communications (APPC) to communicate with other systems in your network?
• Does your AS/400 use TCP/IP to communicate with other systems in your network?
Other questions, such as the following one, prompt you to select from a more general response:
• What is your AS/400 used for?
a) Running business applications
b) Application development
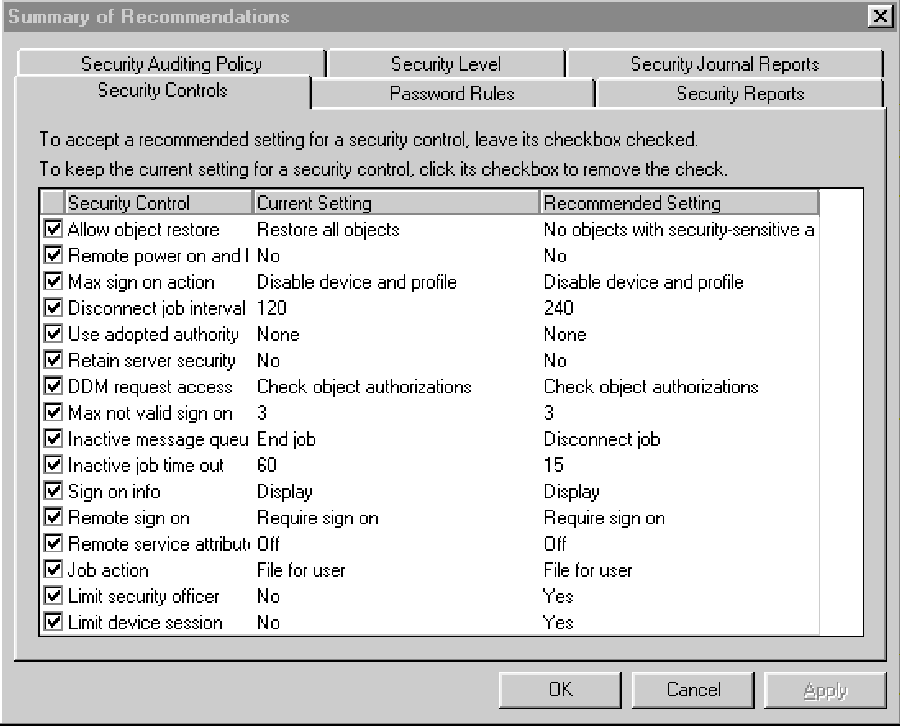
c) Both application development and running business applications When you are finished answering the questions, you will see a panel like the one shown in Figure 2. From this panel, you can either accept the values chosen for you by the wizard, or review those values and optionally override the selections chosen for you by clicking on the Details button. When you click on the Details button, you’ll see the Summary of Recommendation panel like that shown in Figure 3.
The Security Wizard Recommendations
This Summary of Recommendations panel shows you what the System Security Values are, what their current settings are on the AS/400, and what the Security Wizard recommends their new setting should be. If you don’t like the recommendations for a particular setting, click on the check box to unselect it. If you want to keep the recommend setting, do nothing. The value shown here will be set on your AS/400 to the recommended setting when you choose the option to apply these recommendations on a later panel.
As you can see in Figure 3, the various System Values are categorized for you on several panels. For example, all the System Values relating to passwords are grouped under the Password Rules tab, while all the System Values relating to security journal reports are grouped under the Security Journal Reports tab. Having all these values in one spot—along with their current and recommended settings—makes it easy to understand your entire security picture. If you’ve ever modified security System Values from the Work With System Values screen on your AS/400, you’ll really appreciate this approach.
The Recommendations Reports
After you’ve reviewed all the settings, and made any changes, close that panel and you’ll move forward to the Security Reports panel (Figure 4). The Security Wizard provides two types of reports: an Administrator Information report and a User Information report. Both will be written to your PC’s hard drive, and you’ll be given the option of viewing them before you apply any changes.
The Administrator Information report provides information on those System Values that affect signing on to your AS/400. As you scroll through the report, you’ll see the recommendations, which will match what you saw on the Details panel. If the Wizard recommended any changes to current settings, the report may tell you about any associated operational changes you may also need to make.
For example, on my AS/400, the System Value QMAXSIGN (Maximum Sign-on Attempts) was set at •NOMAX. That means I can forget my password 25 times (which is not out of the ordinary for me), and my user profile and device won’t suffer any untoward consequences. The Security Wizard recommended I change this System Value to 3. Because this new value was different from the current value, the wizard generated some informational messages for me in the report. This information included telling me what happens when someone exceeds the number of allowed sign-on attempts as well as what should be done to reinstate the User Profile and the Device if/when they become disabled as a result of this and other System Values. This is useful information, especially for those folks who may not be used to AS/400 security violations.
There is one odd thing about the Administrator report: While it is generated from Operations Navigator, its recommendations on how to go about changing your AS/400’s security values are written for the green-screen environment using the Work with System Values (WRKSYSVAL) command. Given the easy-to-use graphical interface of Operations Navigator and the fact that you are already using Operations Navigator to generate the report, you would think that IBM would steer you toward Operations Navigator for instructions on configuring your AS/400 system security. Perhaps IBM is concerned that people aren’t quite ready to trust Operations Navigator for basic configuration like security, so they gave the instructions in a format the widest possible audience would understand: green-screen. Still, it is rather strange that IBM isn’t encouraging you to use the Operations Navigator tool further while you are in the middle of using the tool.
The User Information report provides information about your System-Wide Security Policy. It is a more human-friendly kind of report than the Administrator Information report. As you read through this document, you’ll find that the information contained in the Administrator Information report has been translated from hard facts into a more conversational format. The following is an excerpt from the User Information report generated by the Security Wizard for my AS/400: “When you sign on to the system, you will see the Sign On Information display. It shows when you last signed on and whether your last sign-on attempt was incorrect (such as an incorrect password). Review the information on the display. If you notice anything that indicates someone else is trying to sign on with your user profile, report it to the security administrator.”
Other sections in the report explain the password rules, as defined by the System Security Values: “To help protect user’s passwords, the system will require you to set a new password every 60 days.”
I found this report to be extremely easy to read and useful. It could even serve as part of your shop’s security documentation. Portions of it would be suitable to be passed out to your users when you assign them user IDs and passwords on your system.
Applying the Recommendations
Applying the security recommendations is as simple as clicking on the box that says, “Yes, make changes now” (see Figure 5). If you select this box, the Operational Navigator will make these changes to your AS/400’s System Security Values immediately. You also have the option of printing the recommendation report(s) and manually making
those changes. This may be desirable if you don’t want to make the changes all at once or if, for example, you don’t want to make these changes in the middle of a day. You can also save these changes and apply them at some later date and time.
That’s all there is to it. The new Security Wizard in Client Access/400 makes being a system security administrator easy and enjoyable. By simply answering a few questions, and reviewing a couple of easy-to-read reports, you can tailor your system’s security to be as tight or as loose as your shop requires.
Figure 1: The new AS/400 Security Wizard from Operations Navigator is shown here.
Enjoy!
 |
 |
 |
 |
 |











 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online