PowerTech Compliance Monitor 3 lets you preview the effect of security level changes.
Each year, PowerTech's popular "State of IBM i Security" study reports on the assigned value of the IBM security system value, QSECURITY. While many systems now are running at the IBM recommended minimum level of 40, there are still numerous organizations that are running at level 30 and even (gasp!) level 20.
A Quick Overview
Let's review some background in case you're not familiar with the QSECURITY system value and the reasons you need to be concerned about it.
IBM i offers five security levels:
- Level 10: No security enforcement, including no password and no requirement for a user profile to exist.
- Level 20: System requires an existing user profile and correct password. By default, all users get *ALLOBJ security authority and *SAVSYS operator privileges.
- Level 30: Same as level 20 except only *SECOFR class profiles get *ALLOBJ special authority by default.
- Level 40: Level 30, plus operating system integrity protection functions.
- Level 50: Level 40, plus additional enhanced integrity protection.
Beginning with V4R3 of the operating system, IBM wisely withdrew support for security level 10. There is no automatic change if you currently are running at that level, but you can no longer change to it. The shipped default also was upgraded to level 40, which is a big contributor to why many shops are meeting the minimum today.
Chapter 2 of the IBM i Security Reference Manual (SC41-5302-11) describes the QSECURITY system value in greater detail, and you should review this document closely as part of your overall IBM i security strategy.
Don't Be Fooled
Ironically, one common mistake that I see auditors make is putting too much emphasis on the security level. While it is an important indicator of security, systems often are a blend of more than one level—especially at security level 20 or 30. This is because these particular levels are heavily influenced by how user profiles are configured. A server operating at level 20 that has had *ALLOBJ and *SAVSYS authorities stripped from its profiles is effectively operating as a level 30 machine (and vice versa.)
Preparing for Change
If you're running below security level 40, most experts recommend an immediate plan for change. Altering the security level consists of modifying the QSECURITY system value and performing an IPL. However, this is not recommended without first reviewing the possible impact of the new level. Though reversing a change involves changing the QSECURITY value again and performing another IPL, this doesn't guarantee any profile customizations are reapplied.
Migrating up from level 20 usually has the most impact as *ALLOBJ and *SAVSYS special authority are removed from any user profile whose user class would not normally assign that authority. This will affect how the user gains authority to objects and to the system operations they can perform.
Changing from level 30 to level 40 or 50 often has minimal impact. The transition is made easier by the fact that IBM i auditing can log integrity violations that will be blocked at the higher levels. This allows you to resolve any potential issues prior to the change.
The Key to Success
Careful planning is the key to success when it comes to changing QSECURITY. Ensure that you understand the effects of any change before users find themselves unable to perform their duties. Research the effect of special authorities being removed from test profiles—especially *ALLOBJ—and check the audit journal for ongoing integrity violations.
Finally, I always instruct clients to back up security data (such as user profiles) and suggest capturing user profile settings to a database file to aid with recovery if there are issues.
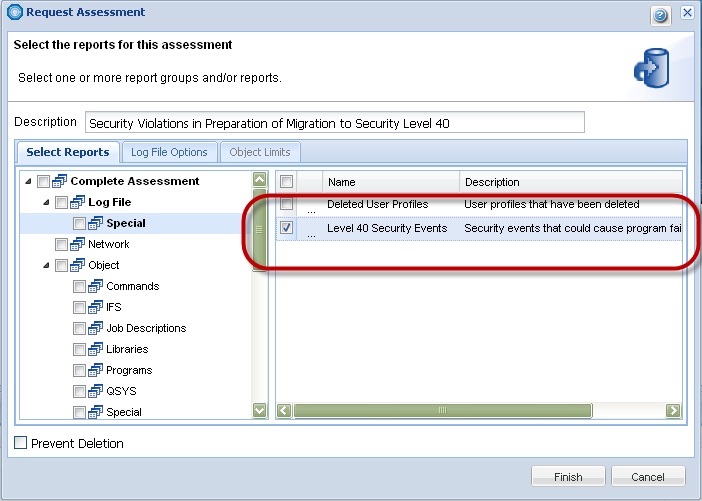
PowerTech Compliance Monitor solves many auditing challenges for IBM i servers, and it includes user and system reports that are extremely useful when it comes to changing security levels. There's even a report that searches the audit journals for level 40 integrity violations! (See Figure 1.)
Figure 1: PowerTech's Compliance Monitor auditing solution contains reports designed to help ready servers for changes to QSECURITY. (Click image to enlarge.)
Next Steps
To see your system security level and to determine whether your user profiles and resource security are undermining it, start with a no-cost PowerTech Compliance Assessment.
If you're new to Compliance Monitor, you can try it free for 30 days. If you're already a Compliance Monitor customer, upgrading to Version 3 is covered by your maintenance agreement. You also can learn more about the new Compliance Monitor by signing up for Help/Systems' Solutions Summit scheduled for September 18–20 in Minneapolis.












 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online