If you have been an AS/400 programmer for any length of time, you have probably heard requests similar to this: “I want you to add an option to the customer inquiry program that will allow me to edit customer records, but I don’t want those gorillas down in the warehouse to be able to use it. They can barely run a forklift, much less a keyboard. I only want our people in accounting to be able to update customer records.”
How did you handle such requests? Did you require that the operator key in a password to be able to edit customer records? More often than not, that password would be known companywide by the time you compiled the program. Did you hardcode error checking into the program based on the user ID? If you did, you now need to change the program every time you add or delete a user profile (if you even remember to do so). Did you copy the customer inquiry program to another program, creating one program for accounting and another for everyone else? This solution has a downside, too: Future maintenance on the program, when performed consistently, would be double the work and twice the headaches.
Think about it. Common sense should tell you that adding a new option to the screen would only invite people to use it. In fact, trying to restrict people from using a new option has to be considered an open invitation to try to find a way to use it. Furthermore, trying to restrict selected operators from using an option just might be perceived a “digital act of war.” Remember: Those “gorillas down in the warehouse” know where you store your lunch, they know where you park your car, and, most importantly, they are the first to handle your new equipment when it arrives. (Is the phrase “damaged during shipping” familiar to you?)
No, we think that perhaps it is best if operators see on the screen only the options they are allowed to use. You know: “Deliver us not into temptation.” This concept is the very premise of this article. We are going to show you how to “softcode” the options on your subfile program so operators can see and use only the options they are authorized to see and use. In addition, the only maintenance you need to perform is maintenance on a file for operators whose options are different from the default.
What You See Is What You Get
For our sample program, we wrote a simple program called Customer Inquiry, which is shown in Figure 1. The options presented on the screen are the only ones the operator is authorized to use, and editing has been put in place that keeps operators from choosing options that do not appear on their screens.
How do you control which options appear on the operator’s screen? This is done by matching the program name and operator’s user ID with records in the OPERATOR file, seen in Figure 2. What makes this particular method relatively painless is that not all operator user IDs need to be keyed into the OPERATOR file; only exceptions to the rule have to be maintained in this file. A default record will be entered into the OPERATOR file. This default record will be used as the common standard for all user IDs not found in the file.
Seeing Is Believing
Figure 3 contains a portion of the display file DDS for the subfile program. This subfile is a simple Customer Inquiry program that allows positioning and performing of options on records in the Customer file. The program uses a logical view of the Customer file sequenced by customer name.
Take a walk through some of the code for the subfile program, which is shown in Figure 4. It begins with the initialization subroutine, *INZSR. When present, this subroutine is always automatically called as part of the program initialization. The first thing the program does is to establish a key list for the OPERATOR file. The GetOptKeys key list comprises the procedure name (SFL101RG in our case) and user ID of the operator running the program. This information is automatically retrieved from the program information data structure (which is defined in the definition specifications) during program initialization. We have included the procedure name as part of the key to the OPERATOR file so this file could be used for any number of programs.
The program “chains” to the OPERATOR file to see whether or not a record with the current program’s procedure name and user ID is found there. Remember that only exceptions need to be maintained in the OPERATOR file. If no such record is found, the program retrieves the record by using DEFAULT as the user ID. When this is the case, the values in the default record are used in lieu of the operator-specific defaults. If neither of those records is found, the program looks for a record with DEFAULT in both the user ID and the procedure name fields.
Whichever the case, the program next builds the subfile option labels by using both the OPTIONS array and the LABELS compile time array. The OPTIONS array simply redefines the options found in the OPERATOR file. The values for the LABELS compile time array can be found at the bottom of the source code for the program. The program matches the allowed options (as defined by the appropriate OPERATOR record) with the matching option labels and builds an output field called OPTLABEL. This field appears in the subfile control record and informs the operator of which options he is allowed to run. For the example in Figure 1, all subfile options have been presented and deemed valid.
Once the option labels have been established, the pointer for the CustomerLF file is set at the beginning of the file and the LoadSfl subroutine is called to build the subfile. The subfile is classified as a page-at-a-time subfile, meaning that a single subfile page is written and then displayed. Subsequent paging or “position to” operations will cause the subfile to be cleared and a new subfile page to be written. The initialization routine is complete, so control of the program is now turned over to the standard program cycle, which is represented by the beginning of the calculation specifications.
We designed the program to “loop” until one of three things happens: “F3=Exit” is pressed, “F12=Previous” is pressed, or Enter is pressed with no selection made. If Page Up is pressed, the program will reset the Customer file pointer by chaining to the Customer record currently displayed at the top of the subfile and then reading backward through the
file until the program has read enough records to write a subfile page. Pressing either Page Up or Page Down will execute the LoadSfl subroutine, whereby control is returned to the program cycle.
Another feature we added to the program is a field that allows the operator to “position to” a specific customer by keying all or part of a customer name and pressing Enter. This “position to” field is called SetPoint. When something is keyed into this field and Enter is pressed, the pointer to the CustomerLF file is reset (with the characters keyed) and the LoadSfl subroutine is executed. Once again, control is returned to the cycle.
You use the Read Changed Record (READC) operation to determine whether or not any option was chosen on the subfile. Since the modified data tag can be “tripped” by pressing the Field Exit key through options, you can ignore any records that have blanks in the option field. Next, you edit any option chosen to determine whether or not it is between 1 and 6. If an option fails this test, you set the error indicator on, update the subfile record (so the cursor is positioned on the record in error), and return control to the cycle. We performed the first edit to avoid an array index error on the second test, which determines whether or not the operator has chosen an option he is authorized to perform by checking the option against the OPTIONS array found in the OPERATOR record. Again, any error found is treated as such, and control is returned to the cycle.
If the selection has passed the edits, you may then perform the chosen option. For brevity, the actual routines used to perform each of these functions have been omitted.
Nobody Knows the Trouble I’ve Seen
Subfiles are flexible; subfiles are powerful; subfiles are your friends. And there is always something new to learn about them or do with them. Open your mind! You may be surprised by what you see.
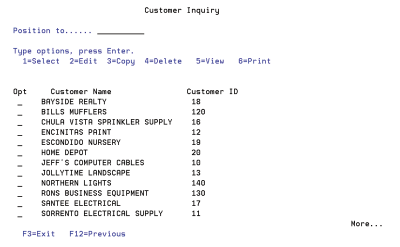
Figure 1: Valid options for this subfile depend on the user.
A R OPERRECORD
A PGMNAME 10 COLHDG(‘PROGRAM NAME’)
A NAME 10 COLHDG(‘OPERATOR NAME’)
A OPTSELECT 1 COLHDG(‘SELECT RECORD’)
A OPTEDIT 1 COLHDG(‘EDIT RECORD’)
A OPTCOPY 1 COLHDG(‘COPY RECORD’)
A OPTDELETE 1 COLHDG(‘DELETE RECORD’)
A OPTPRINT 1 COLHDG(‘PRINT RECORD’)
A OPTVIEW 1 COLHDG(‘VIEW RECORD’)
A K PGMNAME
A K NAME
... (missing code)
*
A R SFLRCD SFL
A SFLOPTION 1 B 10 2DSPATR(HI UL)
A 40 DSPATR(PC)
A SFLCUSTNAM 30A O 10 7
A SFLCUSTID 10A O 10 39
A HDNCUSTNAM 40A O 10 7
*
A R SFLCTL SFLCTL(SFLRCD)
... (more code)
A 40 SFLMSG('Invalid option chosen')
... (more code)
A 3 1'Position to......'
A COLOR(BLU)
A SETPOINT 10A B 3 19
A 5 1'Type options, press Enter.'
A COLOR(BLU)
A OPTLABEL 60A O 6 3COLOR(BLU)
A 9 1'Opt Customer NameA Customer ID'
A DSPATR(HI)
FSfl101Ds CF E WORKSTN SFile(SflRcd:SflRcdNbr)
FCustomerLFIF E K DISK
FOperator IF E K DISK
d sds
d UserID 254 263
d Pgm *proc
d ds
d Options 1 Dim(6)
d OptSelect 1 1
d OptEdit 2 2
d OptCopy 3 3
d OptDelete 4 4
d OptView 5 5
d OptPrint 6 6
d Labels s 8 Dim(6) CTData PerRcd(6)
d GetOut s 1 Inz(*Off)
d Idx s 5 0
c Dou Getout = *ON
* Display/Read Subfile
c MoveA '10' *IN(22)
c ExFmt SFLCTL
* If F3 was pressed, Exit program
c If *InKC = *On
c or *InKL = *On
c Leave
c EndIf
c Eval *In40 = *Off
* Process Page Keys
c If (*In27 = *ON or *In28 = *On) AND
c SflRcdNbr > 0
* If pageup
c If *In27 = *ON
c 1 Chain SflRcd
Figure 2: The options each user is permitted to use are stored in a database file.
Figure 3: This is display file DDS for the softcoded subfile.
c If %found
c HdnCustNam Setll CusRec
c Do 13
c Readp CusRec
c If %Eof(CustomerLF)
c *Loval Setll CusRec
c Leave
c EndIf
c EndDo
c EndIf
c EndIf
c ExSr LoadSfl
c MoveA '00' *IN(27)
c Iter
c EndIf
* Process "Position to" if keyed...
c If SetPoint <> *Blanks
c Eval CustName = SetPoint
c CustName Setll CusRec
c Exsr LoadSfl
c Iter
c EndIf
* Look for Record Selection Request
c Dou *In41 = *ON
c ReadC SflRcd 41
c If %Eof * Enter was pressed without a Request
c Eval GetOut = *ON
c Else *
c If SflOption = *Blanks
c Update SflRcd
c Iter
c EndIf
* Validate the selected operator option
c If SflOption < '1' or SflOption > '6'
c Eval *In40 = *On
c Else
c Move SflOption Idx
c If Options(Idx) <> 'Y'
c Eval *In40 = *On
c EndIf
c EndIf
* Position cursor on the subfile record in error
c If *In40 = *On
c Update SflRcd
c Leave
c EndIf
c Select
* Record was selected
c When SflOption = '1' * Record selected... return customer ID to calling program
c When SflOption = '2' * Call routine to edit customer
c When SflOption = '3' * Call routine to copy customer
c When SflOption = '4' * Call routine to delete customer
c When SflOption = '5' * Call routine to view customer
c When SflOption = '6' * Call routine to print customer
c EndSl
c Clear SflOption
c Update SflRcd
c Iter
c EndIf
c EndDo
c EndDo *
c Eval *InLR = *On
*
CSR *INZSR BEGSR
* Chain to Operator file using the program name current User ID
c GetOptKeys Klist
c Kfld PgmName
c Kfld Name
c Eval PgmName = Pgm
c Eval Name = UserId
c GetOptKeys Chain Operator * If Operator not found, chain to the Default profile
c If NOT %Found(Operator)
c Eval Name = 'DEFAULT'
c GetOptKeys Chain Operator
c If NOT %Found(Operator)
c Eval PgmName = 'DEFAULT'
c GetOptKeys Chain Operator
c EndIf
c EndIf
* Only show operator options he or she is authorized for
c Do 6 Idx
c If Options(Idx) = 'Y'
c Eval OptLabel = %Trim(OptLabel) + ' ' +
c Labels(Idx)
c EndIf
c EndDo
c *Loval Setll CusRec
c Exsr LoadSfl
CSR ENDSR *
CSR LoadSfl BEGSR
* Perform preparatory functions
c Clear SflRcdNbr
c Clear SetPoint
c MoveA '0010' *IN(21)
c Write SFLCTL
c Eval *In23 = *off
c Write Screen1
* Write subfile
c Do 12
c Read CusRec * Get out when there are no more records to read
c if %EOF(CustomerLF)
c Leave
c EndIf
C Clear SflOption
c Eval SflRcdNbr = SflRcdNbr + 1
c Eval SflCustNam = CustName
c Eval HdnCustNam = CustName
c Eval SflCustID = Customer#
C Eval *In21 = *ON
c Write SflRcd
c endDo
c * Set SFLEND indicator if at end of file
c if %EOF(CustomerLF)
c Eval *In24 = *On
c Else * Look ahead and set SFLEND indicator if at end of file
c CustName SetGt CusRec
c if NOT %Found(CustomerLF)
c Eval *In24 = *On
c EndIf
c EndIf
CSR ENDSR
** CTDATA Labels
1=Select2=Edit 3=Copy 4=Delete 5=View 6=Print
Figure 4: Softcoding options require a little more source code, but it’s not complicated.











 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online